|
Conducting an API security assessment involves several steps to identify potential security vulnerabilities, bugs, and flaws in the API code. The following is a general process for conducting an API security assessment:
For more information about our CATSCAN service contact us. Dynamic Application Security Testing (DAST) is a type of security testing that evaluates the security of web applications while they are running. In the context of a service provider selling DAST to a buyer, the service would involve the following steps:
For more information about our CATSCAN service contact us Social engineering is a tactic used by cybercriminals to trick individuals into divulging confidential information. Here are ten common ways social engineers gain access to confidential information:
For more information about our CATSCAN services contact us today I recently did a interview on the Reimagining Cyber Podcast about advancements in the software security industry. I then took some time to think about the Fortify product that I have worked with for so many years. The pro and the con, what are your thoughts? OpenText - FortifyPros of using source code tools like Fortify for software code quality:
Here are some best practices for a small business that has purchased Microsoft Windows Server 2019:
Physical and logical security convergence refers to the integration of traditional physical security measures (such as cameras, locks, and alarms) with computer-based security systems (such as network security, access control, and surveillance). This convergence allows for a more comprehensive and holistic approach to security, as it allows organizations to better protect their assets and personnel by considering both the physical and digital realms.
One of the main benefits of physical and logical security convergence is that it allows for better information sharing between different security systems. For example, an access control system can be integrated with a video surveillance system, so that if a door is opened without proper authorization, a video of the event can be automatically recorded. This can help organizations quickly identify and respond to security breaches. Another benefit of physical and logical security convergence is that it allows for more efficient use of resources. By integrating different security systems, organizations can reduce the number of separate devices and systems that need to be managed and maintained. This can help lower costs and reduce the risk of system failures. One of the main challenges of physical and logical security convergence is that it can be difficult to achieve. This is because different security systems are often developed by different vendors and use different protocols and standards. This can make it difficult to integrate different systems together, and can lead to compatibility issues. Another challenge of physical and logical security convergence is that it can be difficult to manage. This is because as more systems are integrated, the number of variables that need to be considered can increase, making it more difficult to identify and respond to security breaches. Overall, physical and logical security convergence can provide a more comprehensive and holistic approach to security, allowing organizations to better protect their assets and personnel. However, it can be difficult to achieve and manage, and requires careful planning and execution to be successful. VMWare ESXi is a popular virtualization platform for running multiple Windows servers, including Active Directory, file, and print services. Here are some best practices for setting up a VMWare ESXi system for this purpose:
Cisco Meraki is a cloud-managed networking solution that provides a wide range of features and functionalities to help organizations manage their networks. The best practice for configuring Cisco Meraki depends on the specific needs and requirements of the organization. However, there are some general guidelines that can be followed to ensure that the configuration is secure and efficient.
A SonicWall firewall can be configured for optimum security by following these best practices:
icrosoft PowerShell is a powerful tool that can be used to automate various tasks in Azure, including the creation of users. One way to create multiple users in an Azure tenant is by using a .csv file that contains the necessary information for each user. In this tutorial, we will walk through the steps of using PowerShell to create users in an Azure tenant from a .csv file.
By following these steps, you can use PowerShell to automate the creation of multiple users in an Azure tenant from a .csv file. This can save a lot of time and effort compared to manually creating each user, especially if you need to create a large number of users. When it comes to security, it's important for businesses to trust their service providers. Accreditation is a way for businesses to ensure that their service providers are meeting industry standards and that they are providing high-quality services.
One of the main reasons why businesses should buy security services from accredited service providers is that these providers have been independently vetted by a third party. This means that they have been assessed against a set of standards and have been found to meet or exceed those standards. This provides businesses with a level of assurance that they are working with a reputable and trustworthy provider. Another reason why businesses should buy security services from accredited service providers is that these providers have a proven track record of success. Accreditation is not a one-time event; it must be renewed on a regular basis, meaning that providers must continuously meet the standards in order to maintain their accreditation. This means that businesses can trust that their providers have the necessary experience and expertise to provide high-quality security services. Accreditation can also help businesses ensure that their service providers are keeping up with the latest technology and industry developments. Accreditation bodies often require providers to demonstrate that they are using the latest technology and that they are staying up-to-date with industry trends. This helps businesses ensure that their service providers are providing the most current and effective security solutions. Moreover, Accreditation also ensures that the service providers are adhering to the regulations, laws and compliance requirement that are specific to the industry or sector they are operating in. This is especially important for businesses that operate in regulated industries, such as financial services or healthcare, where compliance with regulations is critical to maintaining the trust of customers and stakeholders. Additionally, Accreditation also helps in building trust with the customers and partners. When a business is working with an accredited security service provider, it sends a message to its customers and partners that the business takes security seriously and that it is committed to protecting its own and its customers' assets and sensitive information. In summary, businesses should buy security services from accredited service providers because these providers have been independently vetted, have a proven track record of success, are keeping up with the latest technology and industry developments, adhering to the regulations, laws and compliance requirements and also helps in building trust with the customers and partners. Accreditation is an important way for businesses to ensure that they are working with reputable and trustworthy providers and that they are getting the high-quality security services they need to protect their assets and personnel.
Active Directory (AD) is a critical component of any Windows Server environment, and proper configuration is essential for efficient administration. Here are some best practices for configuring Windows Server 2019 Active Directory for administration:
Small businesses are increasingly becoming the target of cyber attacks, making it important for them to take steps to protect themselves from hackers and social engineers.
Here are 10 things that small businesses can do to protect themselves:
Scoring Matrix
Critical (9.0 – 10.0) Vulnerabilities that score in the critical range usually have most of the following characteristics:
These vulnerabilities can allow attackers to take complete control of your resources. In exploiting this type of vulnerability, attackers could carry out a range of malicious acts including (but not limited to):
On exploiting such vulnerabilities, attackers can access and control logged-in user or administrator accounts, enabling them to hijack accounts and make changes that typically only those users can. Suggested Action for Critical Severity Vulnerabilities A Critical severity vulnerability means that resources can be exploited at any time. It is advised to make it the highest priority to fix these vulnerabilities immediately via patching, upgrading or other mitigation measures. Once a fix action has been implemented, rescan the affected resource to ensure the vulnerability or weakness has been mitigated. High (7.0 – 8.9) Vulnerabilities that score in the high range usually have some of the following characteristics:
On exploiting such vulnerabilities, attackers can view information about your system that helps them find or exploit other vulnerabilities that enable them to take control of your website and access sensitive user and administrator information. Suggested Action for High Severity Vulnerabilities A High severity vulnerability means that resources can be exploited and attackers can find other vulnerabilities which have a bigger impact. Fix these types of vulnerabilities immediately. Once a fix action has been implemented, rescan the affected resource to ensure the vulnerability or weakness has been mitigated. Medium (4.0 – 6.9) Vulnerabilities that score in the medium range usually have some of the following characteristics:
By exploiting Medium Severity Vulnerabilities, attackers will gain information and reconnaissance useful for their attack. Medium Severity vulnerabilities are often used to better understand your system, allowing them to refine and escalate the attacks. Such vulnerabilities can sometimes be connected, to increase the potential damage of the attack. Suggested Action for Medium Severity Vulnerabilities Most of the time, since the impact of Medium severity vulnerabilities is not direct, you should first focus on fixing High severity vulnerabilities. However, Medium severity vulnerabilities should still be addressed at the earliest possible opportunity. Low (0.1 – 3.9)
Do not overly concern efforts towards resources with low severity vulnerabilities. These types of issues do not have any significant impact and are likely not exploitable. Suggested Action For Low Severity Vulnerabilities If time and budget allows, it is worth investigating and fixing Low severity vulnerabilities . Informational
Reported simply as supporting information for a resource, as they may not have a direct impact but could help an attacker to gain a better understanding of your underlying systems. Suggested Action for Informational Alerts In most cases, no action or fix is required. Want to find out how many issues you have? Contact us today and ask about CATSCAN from ProactiveRISK The Gramm-Leach-Bliley Act (GLBA) is a federal law that requires financial institutions, including accounting and CPA businesses, to protect the privacy of customers' nonpublic personal information (NPI). The GLBA safeguard rules provide specific guidelines for how financial institutions should protect this information. Here are some steps that accounting and CPA businesses can take to comply with the GLBA safeguard rules:
Cybersecurity is a critical concern for businesses of all sizes and industries. With the increasing reliance on technology, businesses have become vulnerable to cyber attacks, data breaches, and other forms of cybercrime. The potential consequences of a cyber attack can be devastating and far-reaching, including financial losses, reputational damage, and legal liabilities. Therefore, it is essential that businesses take a proactive approach to managing cyber security risks.
One of the main reasons businesses should be proactive about cyber security risks is that the threat landscape is constantly evolving. Hackers and cybercriminals are constantly developing new techniques and strategies to breach security systems and steal sensitive information. Businesses that do not stay up-to-date with the latest security threats and trends will be more vulnerable to attacks. By being proactive and constantly monitoring the threat landscape, businesses can identify potential vulnerabilities and take steps to mitigate them before they are exploited. Another reason why businesses should be proactive about cyber security risks is that the costs of a cyber attack can be significant. A data breach can result in the loss of sensitive information, such as customer data, financial records, and confidential business information. This can lead to financial losses, legal liabilities, and reputational damage. In addition to the direct costs, businesses may also face indirect costs, such as lost productivity, lost customers, and the need to invest in additional security measures. By being proactive and implementing effective security measures, businesses can reduce the likelihood of a cyber attack and minimize the potential costs. Proactivity also helps to protect your company's reputation. A cyber attack can seriously damage a company's reputation, as customers and partners may lose trust in the company's ability to protect their sensitive information. This can lead to long-term damage to the company's brand, and it may be difficult to regain customer trust once it is lost. By being proactive and implementing effective security measures, businesses can prevent data breaches, protect customer data, and maintain a positive reputation. Additionally, with more and more regulations coming into place, it is important for businesses to be proactive about cybersecurity to avoid the legal and financial consequences of non-compliance. Many states and countries now have laws requiring companies to disclose data breaches, and businesses may face significant penalties for failing to comply with these regulations. By being proactive and implementing security measures that comply with relevant regulations, businesses can avoid legal liabilities and fines. In conclusion, being proactive about cybersecurity is essential for businesses of all sizes and industries. The threat landscape is constantly evolving, and the costs of a cyber attack can be significant. By identifying potential vulnerabilities and implementing effective security measures, businesses can reduce the likelihood of a cyber attack and minimize the potential costs. Proactivity also helps to protect the company's reputation, and it is important to comply with the relevant regulations. Businesses that fail to take a proactive approach to managing cyber security risks will be more vulnerable to attacks and face greater consequences. It is important to remember that cyber security is not a one-time or occasional task, it should be an ongoing process, regularly monitored, and updated. It is difficult to predict exactly what will happen in the field of cybersecurity in 2023, as it is constantly evolving and there are many factors that can influence its development. However, it is likely that there will be a continued focus on protecting against cyber threats and vulnerabilities, and there may be a number of significant developments in the field over the next few years.
Some potential trends in cybersecurity in 2023 could include:
Throughout my career, I’ve listened to and participated in the debate or discussion surrounding security vs compliance. Most often it seems that those involved in the discussion feel as though they need to take one side or the other. That co-mingling the two is more of a necessary evil versus an activity that provides value to the overall security strategy and program. In this blog, we’ll identify the differences between security compliance and security in general and highlight the potential benefits of a robust security compliance program. WHAT IS SECURITYSecurity is a journey. It’s a collection of people, processes, and technologies operating at multiple layers within the organization that should work together to help strengthen a company’s overall security profile and ultimately protect its digital and non-digital assets. While journeys typically include a beginning and an end, I would argue that the security journey has no end. Good luck finding a CISO or security executive who will openly admit that their company has achieved security, or who can truthfully state that they are able to sleep through the night without any concern for the assets they’ve been charged to protect. The task of securing a company’s assets is a daunting endeavor. With the constant barrage of automated alerts, weekly releases of newly discovered vulnerabilities, relentless and never-ending attacks from a growing list of known and unknown bad actors, the challenges posed by external forces appear to be never-ending. Coupled with constant requests from internal teams to use the latest unproven or untested technology and a queue full of internal requests to integrate and share data with external vendors, who can blame today’s security executive for losing sleep. While many battles within the security journey can be won, the security war is endless and rages on with no end in sight. What is IT Security Compliance?IT or security compliance is the activity that a company or organization engages in to demonstrate or prove, typically through an audit, that they meet the security requirements or objectives that have been identified or established by an external party. That list of security requirements could be as simple as a list of security objectives that a customer or business partner deems critical or pertinent to the established or proposed business relationship. It could also represent a much more complex and lengthier list of controls and objectives (i.e. security framework) which has been established by external professional organizations, specific industries, or government agencies. It’s easier for a company, customer, or business partner to adopt an industry-recognized framework versus establishing their own set of criteria however some companies may have a framework dictated to them based on the industry they operate in or regulatory obligations, i.e. Payment Card Industry, Healthcare, DOD, etc. Recognized and established third party security frameworks, certifications or reports can include but are not limited to, ISO’s 27001, NIST’s 800-53, PCI, HIPAA, and SOC 2 reports. The resulting certifications or reports demonstrate to customers, business partners (i.e. user organizations) and potential regulators that the company or service organization has achieved compliance, per the opinion of an independent auditor, with the stated security controls and objectives identified within the applicable framework. Demonstrating compliance with a recognized security report or certification helps relieve the burden from the service organization of having to open its doors to multiple auditors from several different user organizations that may want to validate the service organization’s security operations. It can also simplify a user organization’s vendor management process by being able to place reliance on the work of an independent auditor versus having to build out or expand their own technical audit team. Does Compliance Equal Security?Yes and no. Passing a security audit or obtaining a certification or a report that demonstrates your organization complies with an industry-accepted security standard or framework is a big deal. It definitely adds value and strengthens the overall security program. Depending on the certification obtained, the achievement demonstrates that a company has invested time, money, and resources into its people, processes, and technology to both design, implement and operate in accordance with a defined security framework. It is important to remember however that security compliance standards or frameworks aren’t a one size fits all and aren’t all-encompassing. It would be an impossible feat for one organization, regulatory body, or agency to define a security framework that identifies and mitigates all security risks for every company that chooses to adopt it. No two company’s security risk profile or technology landscape are the same. A security framework attempts to establish a baseline or identify a high-level suite of control activities that are applicable to all organizations regardless of their size, technology footprint, or industry. In other words, IT compliance frameworks help to establish an excellent security foundation for additional security activities that a company should engage in based on identified risks, to secure their organization. So yes, security compliance absolutely helps a company establish, strengthen, and add value to its Information Security Management System. However, the security journey will require additional effort beyond the baseline control activities identified in a security framework. How Can Security Compliance Help My Company?Security compliance can identify gaps in a security program. Some security practitioners may have a difficult time identifying the benefits of security compliance within their security program. In their minds, security compliance may act more as an inhibitor to the company’s progress and efficiency rather than as a benefit. While strong security programs can be established without compliance, at times, some of the more foundational or baseline security controls can be overlooked or forgotten. This is typically the result of increasing demands being placed on security organizations and the need to place more focus on some of the more complex security risks facing a company. For those organizations that aren’t required to adhere to a compliance framework, it has proven beneficial to perform a gap assessment against a recognized compliance standard. This validates if their security program addresses all identified baseline security controls. It can prove to be an eye-opening experience when potential gaps or areas for improvement are identified. Why is Security Compliance Important?Security compliance also helps to establish governance, formality, ownership, and accountability within your security program. Sometimes, security compliance may be referred to as a burden or a waste of time. However, the documentation requirements surrounding policy, procedure, frequency, and preservation of evidence should help to establish confidence that security objectives and control activities are uniformly understood throughout the organization and that assignments or ownership have been designated and defined. Clearly defined ownership surrounding risks, controls, and data also helps to establish accountability which instills more confidence in a team’s ability to execute against state objectives. Security Compliance – The Importance of ReportingSecurity compliance reporting provides an effective and formal method to measure and evaluate performance against stated control objectives that otherwise may not occur. Again, the reporting should be considered an all-encompassing reflection of all security activities and initiatives within the company, but it should act as an effective report card regarding performance against the baseline set of controls identified by the adopted framework. When compliance with stated security objectives is measured and reported on via compliance reporting, a clearer picture can be established as to what areas of the security program may require more focus and attention, which further helps to prioritize and perhaps realign resources. Compliance with a recognized security standard also helps strengthen a company’s reputation within the marketplace and continues to become the norm for business relationships as more scrutiny continues to be placed on a company’s internal security practices, their sub-service provider’s and those they choose to share data with. Compliance with a recognized security standard becomes even more critical when the data being processed includes PII, PCI, or PHI as the number of different privacy and security regulations continues to grow. ConclusionTo sum it up, security compliance is not the be-all-end-all security silver bullet that at times it may be made out to be. Establishing an effective security program will require additional effort above and beyond demonstrating alignment with an applicable security framework. However, while achieving compliance with a security framework doesn’t represent the completion of the security journey, it does complement and provide several benefits to a company’s overall security program. It can demonstrate to external parties that security has been established as a critical component of the company’s overall business objectives and strategy.
Proactive Risk is an independent assessment firm that specializes cyber security. If you have any additional questions or are interested in retaining our services, please contact us.  I received a call this week from a fortune 500 business, they organization had a problem and wanted to do a meeting related to cyber security centrality analyst. I suggested that we engage with our standard agreement and schedule time to meet and go over the matter details. Although we have published lots of guides and tools for FREE online there was a expectation that all knowledge and experience is "free". The experience reminded me of the story of "The Giant Navy Ship" A giant ship engine failed. The ship’s owners tried one expert after another, but none of them could figure but how to fix the engine. Then they brought in an old man who had been fixing ships since he was a young. He carried a large bag of tools with him, and when he arrived, he immediately went to work. He inspected the engine very carefully, top to bottom. Two of the ship’s owners were there, watching this man, hoping he would know what to do. After looking things over, the old man reached into his bag and pulled out a small hammer. He gently tapped something. Instantly, the engine lurched into life. He carefully put his hammer away. The engine was fixed! A week later, the owners received a bill from the old man for ten thousand dollars. “What?!” the owners exclaimed. “He hardly did anything!” So they wrote the old man a note saying, “Please send us an itemized bill. The man sent a bill that read: Tapping with a hammer………………….. $ 2.00 Knowing where to tap…………………….. $ 9,998.00 Effort is important but knowing where to make an effort makes all the difference! For an IT managed services company to effectively take over the helpdesk, operations, and security for a small business with 10-1000 devices as example, several key items and levels of access will need to be provided. This ensures the service provider has all the necessary tools and permissions to manage your IT infrastructure efficiently and securely.
Here's a general checklist:
We invite you to download our complimentary Cybersecurity Checklist or explore our managed service, ManageIT, by ProactiveRISK for more detailed information. The Federal Trade Commission recently amended the Safeguards Rule, 16 C.F.R. § 314.1, et seq., with significant changes to how an information security program should be designed, what it must include, and who needs to be in charge. Some may note the similarity to the New York Department of Financial Services’ Cybersecurity Requirements for Financial Services Companies, N.Y. Comp. Codes R. & Regs. tit. 23, § 500.00, et seq.
The Rule is now considerably lengthier, but not all the amendments added anything new or substantive. In this article we will explain which changes look new but are not, which are new and substantial, which do not apply to small businesses, and when certain provisions go into effect. THE RULE The Rule was promulgated under the Gramm-Leach-Bliley Act which, in part, requires the FTC to issue rules setting forth standards that financial institutions must implement to safeguard certain information. The Rule applies to customer information held by non-banking financial institutions and “sets forth standards for developing, implementing, and maintaining reasonable administrative, technical, and physical safeguards to protect the security, confidentiality, and integrity of [that information].” The Rule provides this non-inclusive list of entities that are considered financial institutions under the Gramm-Leach-Bliley Act and subject to the rule:
THE AMENDMENTS The amendments to the Rule became effective Jan. 10, 2022, although some of the most important provisions are not effective until Dec. 9, 2022. The FTC summarized the highlights as providing:
WHAT’S NOT NEW Section 314.1 – Purpose and Scope. Although amended subsection (b) appears significantly lengthier, it simply incorporates the definition of “financial institution” from the Privacy Rule, as modified and with examples, “to allow the Rule to be read on its own, without reference to the Privacy Rule.” Section 314.2 – Eleven Old Definitions. Previously, the Rule had only three defined terms and a general provision explaining that the terms used in the Rule had the same meaning as those defined in the Privacy Rule, 16 C.F.R. § 313.3. Now, the Rule has 18 defined terms, but the majority have been carried over from the Privacy Rule to “improve clarity and ease of use.” The Rule’s pre-amendment terms and those carried over from the Privacy Rule without substantive change are:
WHAT’S NEW Section 314.2 – Seven New Definitions. As mentioned above, most of the defined terms are newly added to this section but not new to the Rule because they were previously cross-referenced to their definitions in the Privacy Rule. Following are the seven new terms, and one that has been modified:
Section 314.6 – Exceptions. This “small business” section identifies certain provisions of § 314.4 that “do not apply to financial institutions that maintain customer information concerning fewer than five thousand consumers.” Those provisions are identified below. WHAT’S HOT Section 314.4 – Elements. This section has been completely overhauled, and now explains with specificity the elements, new and old, that must be included in an information security program. Except where indicated, these elements must be incorporated by Dec. 9, 2022. In summary, the elements checklist includes:
COMPLIANCE The elements described in § 314.4 are not new concepts and many entities are already compliant. However, because the elements are now far more specific and detailed than before, we recommend those subject to the Rule compare its elements to those of their own programs to ensure compliance, leaving time for compliance by Dec. 9, 2022.
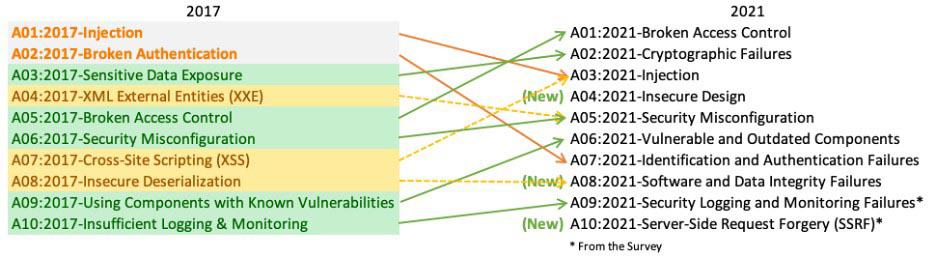
 Published in CPO Magazine April 6th 2022 Post-COVID, a growing number of mid-sized businesses are merging with and acquiring other companies to adapt, grow and expand. This process takes a tremendous amount of preparation and research. From business financials and intellectual property to contracts and tax issues, there is much to be done to help ensure a successful M&A transaction. Among top considerations during the M&A process should be your technical controls. In specific, you need to pay close attention to the software bill of materials (SBOM), and several other vital areas of your technology-enabled business. If the target organization cannot demonstrate technical maturity, it will be score lowered and may ultimately see a reduced acquiring offer or be a deal-breaker altogether. During the due diligence process, be prepared to present and describe your software-based technology product with documentation. What is expected during a technical due diligence review is architectural diagrams, scalability, and performance metrics. Technology choices made, including programming languages, databases, and infrastructure choices, will be reviewed. Your key staff must also be able to describe any software development practices and provide details on continuous deployment environments.. In particular, a review of the OWASP Top 10 2021 List is recommended. Be certain that you are able to answer questions about how you ensure code quality in a hostile internet-connected environment and perform an independent third party code audit Depending on the reason for the merger or acquisition, it could be equally important to have technical controls in place for the operations side of the business. Here it’s important to evaluate how data is processed in 17 key areas:
Remember – confidentiality, integrity and availability are important items of consideration for your technology choices from day one. Be certain to use company that has been accredited to perform valuable third-party assessments with proven policies, processes and procedures to validate your technology and environment. With a credible third-party validation of your technical maturity, you can ensure that the technical elements of your due diligence will enhance acquisition offers and simplify the integration process.
For more information, contact us on how we can help you be proactive. Published in Information Security Buzz
Scrutiny over data protection and privacy, and the reporting and analysis behind a powerful threat defense, is moving to the boardroom as organizations are seeing the need to take a closer look at just how effective their security posture is. In a report, Gartner labels it ‘A New Era of Risk Reporting to the Board,’ noting that “Board members are increasingly aware and concerned about the importance of information security.” Gartner also notes that discussions have evolved from standard security metrics to understanding the enterprise-wide ramifications of information security risks. Boards are now expecting analysis and reporting of the organization’s cyber resilience at the same level as other formal mandatory reporting and company controls. However, executing a cyber resilience strategy is easier said than done, particularly for small or mid-sized businesses that do not have the skills or expertise in house, or large organizations that are dealing with legacy or complex, interconnected business models. Aligning Controls with the Threat Landscape Historically, security controls used to monitor the output and efficiency of a company have been traditionally based around the areas of policy, process procedures and management, along with technical, physical and personnel metrics. In today’s world of constant cyber threats, although these areas are still valid, they must be reinforced with the ability to consider the context of the controls in relation to threats to which the organisation is exposed. This context is provided by the results of cyber incident responses, the exchange of cyber-attack information via information exchanges, CERTS (Computer Emergency Response Teams) and the fast-emerging threat intelligence industry. The additional information provides the ability to review and consider all the controls in the context of the current threat landscape. Then, it is possible to justify new spend to deploy appropriate controls to further mitigate risk. For the first time, the availability of this almost real-time threat information allows security teams to react to a change in threat and prevent a breach. This is a better response strategy rather than waiting for a successful attack or simply trying to contain a threat once the network flags anomalous behavior. Although an abundance of information is becoming available on how to protect a business, the issue is: what is considered as effective and can demonstrate that the business has taken the appropriate action to protect itself and any personal data? Analyzing security options from this perspective of corporate governance will form the basis for building a cyber security resilient operation. An example of why this is important has been the growth of controls covering health and safety. Mandatory compliance regulations and reporting are now standard practice. Should there be a serious health and safety issue the mandatory reports are used to provide evidence of best practices and help demonstrate compliance. This has not only helped to protect people but has also become part of the corporate culture. Taking Corporate Responsibility for Cyber Resilience Assessing the business value of cyber resilience comes in several forms. A privacy breach, for example, can damage customer goodwill for the long term. Compliance violations and fines can damage the confidence of stakeholders and even impact board tenure. Gartner notes that organizations need to create their own value chain, looking at the continuum of security/risk dependencies, IT dependencies, business process and business outcomes and determining the causal relationships connected to each dependency. The message is, reporting tied to business value needs this level of analysis to support board evaluation of risk and to determine risk tolerance. In parallel, the cyber security industry is now working with regulators and businesses alike to develop the concept of a set of formal statements around cyber resilience to provide evidence of best practices and proportionality, backed up by standards, technical assessments, maturity models and a number of other relevant metrics. These documents will then be signed off by suitably credentialed professionals from within the cyber security industry and combined to provide an overall opinion on the company’s cyber security resilience. By more extensive risk reporting and analysis and standardizing on cyber resilience criteria within the security industry, boardrooms will be able to make better informed assessments of their company’s risk posture and plan more carefully for investments for a more secure future. What are your thoughts on the topic? |
CategoriesTom BrennanThis is my blog, there are many like it but this one is mine. Enjoy. BLOG Archives
June 2024
|
|
Protecting Your Business with People, Process, and Technology
© COPYRIGHT 2024. ALL RIGHTS RESERVED. |


 RSS Feed
RSS Feed