Adversary Emulation
|
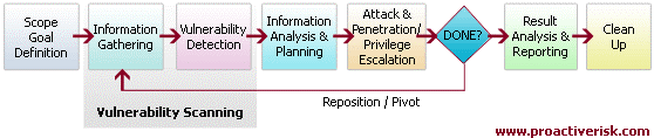
When used in a hacking context, a red team is a group of white-hat hackers that attack an organization's digital infrastructure as an attacker would in order to test the organization's defenses (often known as "penetration testing"). When we assemble our Adversary Emulation team to perform a multi dimensional comprehensive assessment, we call it a CATSCAN® and follow a repeatable framework/methodology
Phase I - Reconnaissance A critical phase in a CATSCAN® project focuses on collecting information about infrastructure, facilities, and employees. The team becomes laser focused on gathering as much information as possible about the target(s). Open Source Intelligence Gathering can be quite telling about a target, its people, its facilities and its technical makeup, such as: physical/logical security controls, foot traffic, terrain, infiltration and ex-filtration points, etc. |
Phase II - Weaponization
Effective weaponization involves preparation of the operation unique to the target taking into full account intel gathered from the reconnaissance stage. This commonly includes: crafting custom file payloads, prepping RFID cloners, configuring hardware trojans, acquiring social engineering costumes, creating falsified personas/companies and much more.
Phase III - Delivery
The Delivery stage is a critical stage of the execution phase. This marks the active launch of the operation in totality. Here, Consultants carry out the actions on the target(s) intended to reach the CATSCAN® Operation’s goals. Things like physically cloning badges, social engineering face-to-face targets, analyzing cyber vulnerabilities, planting hardware trojans for remote network persistence, etc. Among one of the most important objectives is to note the best opportunities for exploitation.
Phase IV - Exploitation
Exploitation during a CATSCAN® project is exactly what it sounds like. At this point, the goal is to “break in” or compromise servers/apps/networks, bypass physical controls (ie: gates, fences, locks, radar, motion detection, cameras) and exploit target staff through social engineering by face-to-face, email, phone, fax or sms. The exploitation stage enables the preparation for the escalation and installation phase.
Phase V - Installation
The installation stage’s primary goal is to prepare for persistence. This could amount to cyber persistence or physical persistence, although cyber persistence is generally slightly more common. During this stage, we establish a beachhead by taking advantage steps taken in the exploitation step. Things like privilege escalation on compromised servers, shells, malicious file payload installation, usage of physical key impressions and lockpicked doors happen here.
Phase VI - Command & Control
Maintaining persistence is the goal for Command & Control. Also generally cyber-focused, ProactiveRISK takes steps to ensure remote access to exploited systems are stable and reliable setting the stage for data exfiltration and other post-exploitation tasks/goals. On the physical and social side, manipulating people into enabling circumvention of physical barriers in order to create backdoors into facilities are key.
Phase VII - Actions on Objective
During this phase of a CATSCAN® project, the team aims to complete the mission and realize the agreed-upon objectives set by the client and ProactiveRISK Security. Actions on objective happen through lateral movement throughout the cyber environment as well as the physical facilities. Pivoting from compromised systems and from breached physical security controls all along capturing video, audio and photographic evidence supporting each finding discovered.
Ultimately, the team aims to exfiltrate data, information or physical assets the target deems critically sensitive.
Effective weaponization involves preparation of the operation unique to the target taking into full account intel gathered from the reconnaissance stage. This commonly includes: crafting custom file payloads, prepping RFID cloners, configuring hardware trojans, acquiring social engineering costumes, creating falsified personas/companies and much more.
Phase III - Delivery
The Delivery stage is a critical stage of the execution phase. This marks the active launch of the operation in totality. Here, Consultants carry out the actions on the target(s) intended to reach the CATSCAN® Operation’s goals. Things like physically cloning badges, social engineering face-to-face targets, analyzing cyber vulnerabilities, planting hardware trojans for remote network persistence, etc. Among one of the most important objectives is to note the best opportunities for exploitation.
Phase IV - Exploitation
Exploitation during a CATSCAN® project is exactly what it sounds like. At this point, the goal is to “break in” or compromise servers/apps/networks, bypass physical controls (ie: gates, fences, locks, radar, motion detection, cameras) and exploit target staff through social engineering by face-to-face, email, phone, fax or sms. The exploitation stage enables the preparation for the escalation and installation phase.
Phase V - Installation
The installation stage’s primary goal is to prepare for persistence. This could amount to cyber persistence or physical persistence, although cyber persistence is generally slightly more common. During this stage, we establish a beachhead by taking advantage steps taken in the exploitation step. Things like privilege escalation on compromised servers, shells, malicious file payload installation, usage of physical key impressions and lockpicked doors happen here.
Phase VI - Command & Control
Maintaining persistence is the goal for Command & Control. Also generally cyber-focused, ProactiveRISK takes steps to ensure remote access to exploited systems are stable and reliable setting the stage for data exfiltration and other post-exploitation tasks/goals. On the physical and social side, manipulating people into enabling circumvention of physical barriers in order to create backdoors into facilities are key.
Phase VII - Actions on Objective
During this phase of a CATSCAN® project, the team aims to complete the mission and realize the agreed-upon objectives set by the client and ProactiveRISK Security. Actions on objective happen through lateral movement throughout the cyber environment as well as the physical facilities. Pivoting from compromised systems and from breached physical security controls all along capturing video, audio and photographic evidence supporting each finding discovered.
Ultimately, the team aims to exfiltrate data, information or physical assets the target deems critically sensitive.